Network Security Audit and Digital Forensics Design Guide
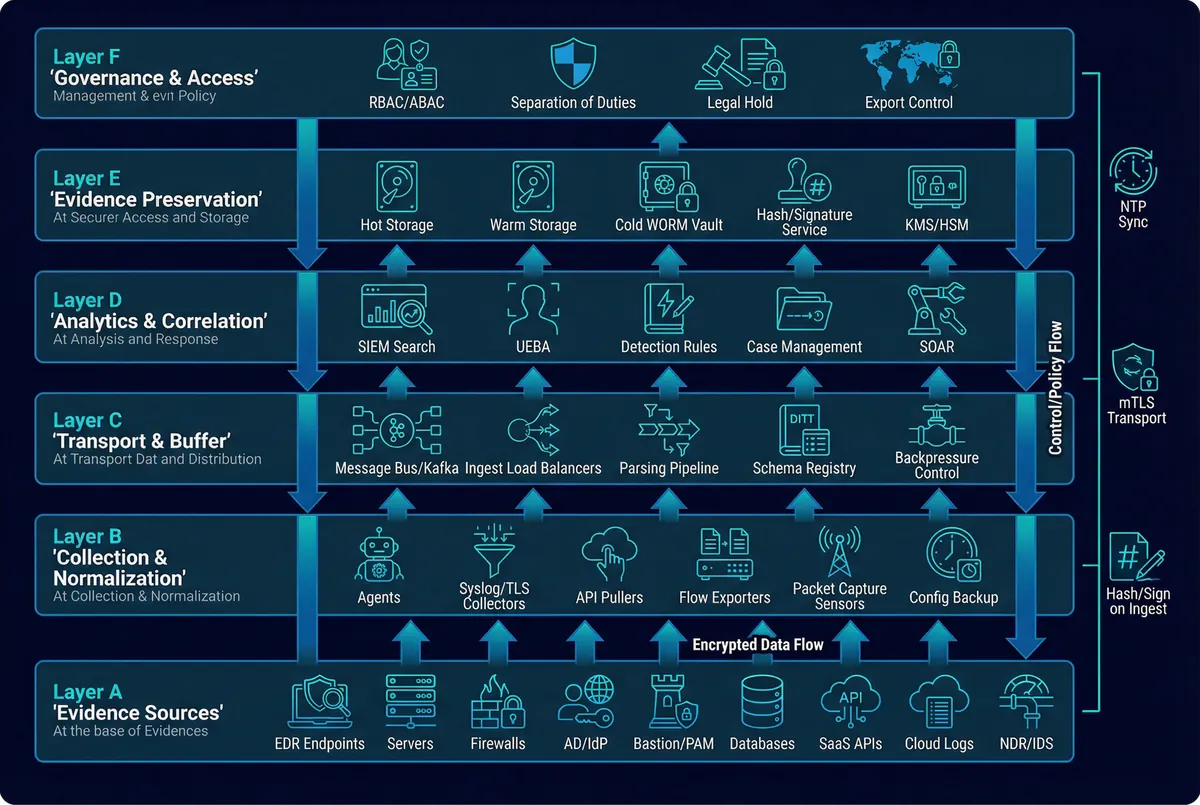
A comprehensive engineering blueprint for building a defensible evidence chain across identity, authorization, operations, configuration change, and security alarms — enabling rapid incident reconstruction and legally defensible compliance proof.
System Overview
Network Security Audit & Forensics Design is an engineering blueprint for building a defensible evidence chain across identity, authorization, operations, configuration change, critical business access, and security alarms — so that incidents can be quickly located, reconstructed, and proven for compliance or legal proceedings.
This system is a cross-domain capability spanning IAM, PAM/bastion, endpoints (EDR), network controls (FW/WAF/proxy/NDR), infrastructure platforms (AD, DNS, DHCP, hypervisors, containers), business systems (ERP/CRM/core apps), and the central log/SIEM/evidence vault. It focuses on three core pillars: Audit Coverage (who did what, when, where, on which asset, with what result), Forensic Readiness (pre-positioned evidence points and standardized collection procedures), and Evidence Integrity (encryption, least privilege, segregation of duties, immutability, chain of custody, retention/archival).
The system targets enterprise environments with 500–20,000 endpoints in hybrid deployments (on-prem DC + cloud workloads + remote endpoints) with a central SOC. Baseline compliance covers ISO 27001/27002, SOC 2, PCI DSS, and applicable local cyber/data regulations. Core value delivered includes fast root-cause reconstruction, reduced dispute risk, improved regulator/auditor confidence, and an operationally repeatable way to produce evidence-grade materials.
Main Functions
The Audit & Forensics Platform delivers eight integrated core functions that together form a complete evidence lifecycle management capability. Each function addresses a specific dimension of audit coverage and forensic readiness, from initial identity verification through final compliance reporting and drill validation.

| Function | Core Value | Key Implementation | Acceptance Focus |
|---|---|---|---|
| Identity & Access Auditing | Ties actions to real identities across systems | IdP/AD logs + MFA + VPN + SSO audit APIs; normalize to single schema | Unique user IDs, MFA outcomes, source IP/device binding, time sync |
| Privileged Operation Recording | Proves admin actions, reduces disputes | Bastion with MFA, command logging, full RDP/SSH recording, keystroke metadata | Tamper resistance, searchable session metadata, exportable replay |
| Configuration Change Tracking | Quick diff of "what changed" during incidents | Config backup + version locking + signed snapshots (network devices, servers, cloud IaC) | Schedule, coverage, restore test, signed diffs |
| Central Log Normalization | Consistent fields enable correlation and reconstruction | Parsing pipelines, schema registry, asset/account mapping, NTP alignment | Field completeness %, parsing error rate, enrichment hit rate |
| Evidence Preservation (WORM) | Makes evidence defensible months/years later | Object lock, WORM, KMS/HSM, periodic integrity scans, legal holds | Immutability proofs, retention enforcement, export verification |
| Network Telemetry & PCAP | Reconstruct lateral movement and exfiltration | NetFlow/IPFIX everywhere feasible; PCAP at egress + critical zones with triggers | Coverage, sampling rates, time correlation with endpoint events |
| Forensic Workflow & Custody | Repeatable and auditable evidence handling | Case IDs, sealed packages, custody logs, role separation | Custody completeness, approvals, immutable audit of the audit system |
| Reporting, Drills & Compliance | Validates readiness before an incident | Monthly audit reports, quarterly reconstruction drills, KPI dashboards | Drill success rate, MTTR for reconstruction, evidence export time |
Chapter Navigation
This guide is organized into twelve chapters covering the full lifecycle of network security audit and digital forensics design, from system components and architecture through installation, operations, and maintenance.