Selection & Interfaces
Core product selection criteria, interface specifications, connection logic, and the comprehensive product function table for all platform components.
5.1 Core Product Introduction
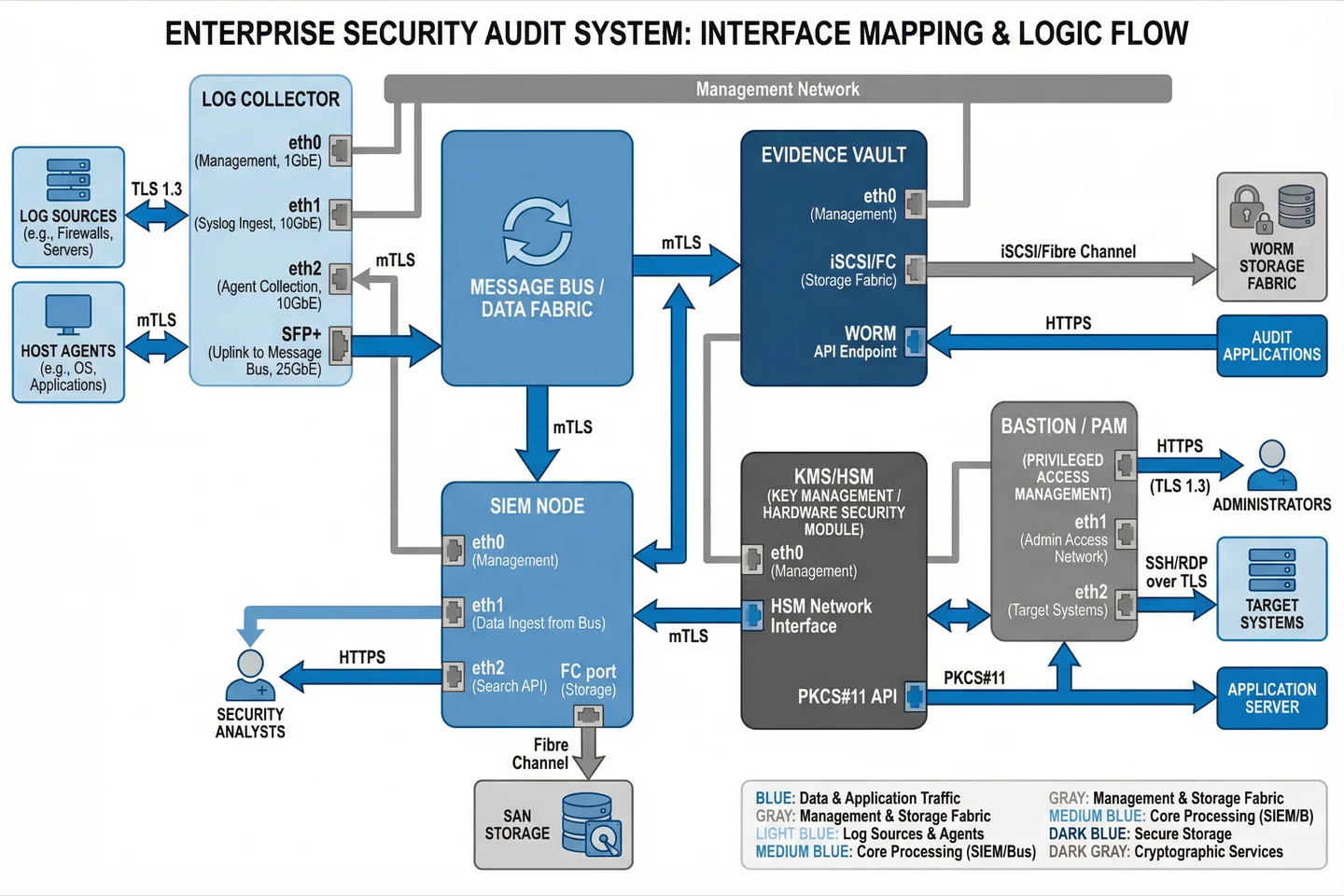
The audit and forensics platform is built from six core product categories, each addressing a specific function in the evidence lifecycle. Product selection within each category should be based on the key selection criteria defined below, with particular attention to integration compatibility, performance under peak load, and evidence integrity guarantees. The following image provides a visual overview of all six core product categories with their primary capabilities.

Core Product Function Table
| Product Category | Primary Functions | Key Interfaces | Critical Selection Criteria | Typical Form Factor |
|---|---|---|---|---|
| SIEM Platform | Event correlation, detection rules, hot index search, dashboards, case management, alert triage | REST API, syslog/TLS ingest, STIX/TAXII threat intel, SOAR webhook, LDAP/SSO | EPS capacity, search latency <5s for 90-day index, schema flexibility, RBAC granularity | Software cluster (3–24 nodes) or SaaS |
| PAM/Bastion Server | MFA-enforced privileged access, full session recording (SSH/RDP/web), keystroke logging, session replay, command approval workflow | SSH proxy, RDP gateway, HTTPS admin portal, LDAP/AD integration, SIEM syslog output | Recording tamper resistance, session search/replay speed, concurrent session capacity, WORM export | 1U appliance or VM (HA pair) |
| Evidence Vault / WORM Storage | Immutable object storage, retention policy enforcement, legal hold, integrity scanning, signed manifests, export packaging | S3-compatible API, NFS/CIFS (optional), HTTPS management, KMS integration for encryption | Object lock compliance mode, retention enforcement bypass prevention, integrity scan frequency, export verification | 2U+ storage array or cloud object store (S3/Azure Blob) |
| Log Collector Appliance | Multi-protocol ingest (syslog/TLS, Beats, WinRM, SNMP), local buffering/spooling, first-stage parsing, mTLS transport to bus | Syslog UDP/TCP/TLS, Beats protocol, WinRM, SNMP trap, REST API pull, SFP+ uplink | Ingest EPS capacity, spool duration (≥24h), drop rate <0.1%, hot-swap power supplies | 1U appliance (N+1 deployment) |
| KMS / HSM Appliance | Key generation and lifecycle management, evidence signing (SHA-256/RSA-4096), PKCS#11 interface, FIPS 140-2 Level 3 compliance | PKCS#11, REST/KMIP API, HSM network interface, management HTTPS | FIPS 140-2 Level 3 certification, signing throughput, key backup/recovery procedures, audit logging of all key operations | 1U HSM appliance (HA pair) |
| NDR / PCAP Sensor | Network traffic analysis, full packet capture, NetFlow/IPFIX generation, protocol decoding, anomaly detection, trigger-based extended capture | Passive TAP or SPAN port, management Ethernet, storage interface for PCAP offload, SIEM alert output | Line-rate capture at target bandwidth, PCAP storage capacity, time correlation accuracy (≤1ms), trigger/filter capabilities | 1U appliance or software on server with TAP NIC |
5.2 Interface Connection Logic
The interface connection logic defines the precise data flow paths, protocol specifications, and security controls for each inter-component connection. This diagram and the accompanying table serve as the authoritative reference for network configuration, firewall rule design, and acceptance testing of all platform interfaces.
| Source Component | Destination Component | Protocol | Port | Security Control | Direction |
|---|---|---|---|---|---|
| Log Sources (servers, FW, apps) | Log Collector eth1 | Syslog/TLS | TCP 6514 | mTLS client cert, IP allowlist | → Inbound |
| Host Agents (EDR, Beats) | Log Collector eth2 | Beats protocol | TCP 5044 | mTLS, enrollment token | → Inbound |
| Log Collector SFP+ | Message Bus | Kafka protocol | TCP 9093 | mTLS, SASL/SCRAM | → Outbound |
| Message Bus | SIEM Node eth1 | Kafka consumer | TCP 9093 | mTLS, consumer group auth | → Outbound |
| Message Bus | Evidence Vault WORM API | HTTPS/S3 | TCP 443 | mTLS, IAM role-based access | → Outbound |
| SIEM Node eth2 | Security Analysts | HTTPS | TCP 443 | TLS 1.3, SSO/MFA, RBAC | → Outbound |
| SIEM Node FC port | SAN Storage | Fibre Channel | N/A | FC zoning, LUN masking | ↔ Bidirectional |
| KMS/HSM PKCS#11 | Evidence Vault | PKCS#11/KMIP | TCP 5696 | mTLS, HSM PIN, role separation | → Outbound |
| Administrators | Bastion/PAM eth1 | HTTPS/SSH | TCP 443/22 | TLS 1.3, MFA, IP allowlist | → Inbound |
| Bastion/PAM eth2 | Target Systems (Zone 1) | SSH/RDP over TLS | TCP 22/3389 | Session recording, command filter | → Outbound |
5.3 Selection Criteria by Deployment Scale
Product selection specifications vary significantly by deployment scale. The table below provides concrete selection thresholds for each product category across the three deployment scales defined in Chapter 4. These thresholds should be used as minimum requirements in procurement specifications and acceptance test criteria.
| Product | Small (<2K endpoints) | Medium (2K–8K endpoints) | Large (>8K endpoints) |
|---|---|---|---|
| SIEM Platform | 10K EPS sustained; 50K EPS burst; 20TB hot storage | 40K EPS sustained; 200K EPS burst; 80TB hot storage | 100K EPS sustained; 500K EPS burst; 200TB+ hot storage |
| PAM/Bastion | 50 concurrent sessions; 1TB recording storage | 200 concurrent sessions; 5TB recording storage | 500+ concurrent sessions; 20TB recording storage |
| Evidence Vault | 50TB WORM capacity; 2-node mirror | 200TB WORM capacity; 4-node erasure coded | 500TB+ WORM capacity; 6+ node erasure coded |
| Log Collector | 2 nodes × 15K EPS each; 48h spool | 4–6 nodes × 20K EPS each; 72h spool | 8–16 nodes × 25K EPS each; 72h spool per site |
| KMS/HSM | 1 HA pair; FIPS 140-2 L3; 100 sign/sec | 1 HA pair; FIPS 140-2 L3; 500 sign/sec | 2 HA pairs (geo-redundant); FIPS 140-2 L3; 2000 sign/sec |
| NDR/PCAP Sensor | 2 sensors at 1Gbps each; 7-day PCAP | 4 sensors at 10Gbps each; 14-day PCAP | 8+ sensors at 10–40Gbps each; 30-day PCAP |