Support & Integration
Supporting system requirements, integration specifications, and dependency management for the eight key systems that the audit and forensics platform relies on for complete functionality.
7.1 Supporting System Ecosystem
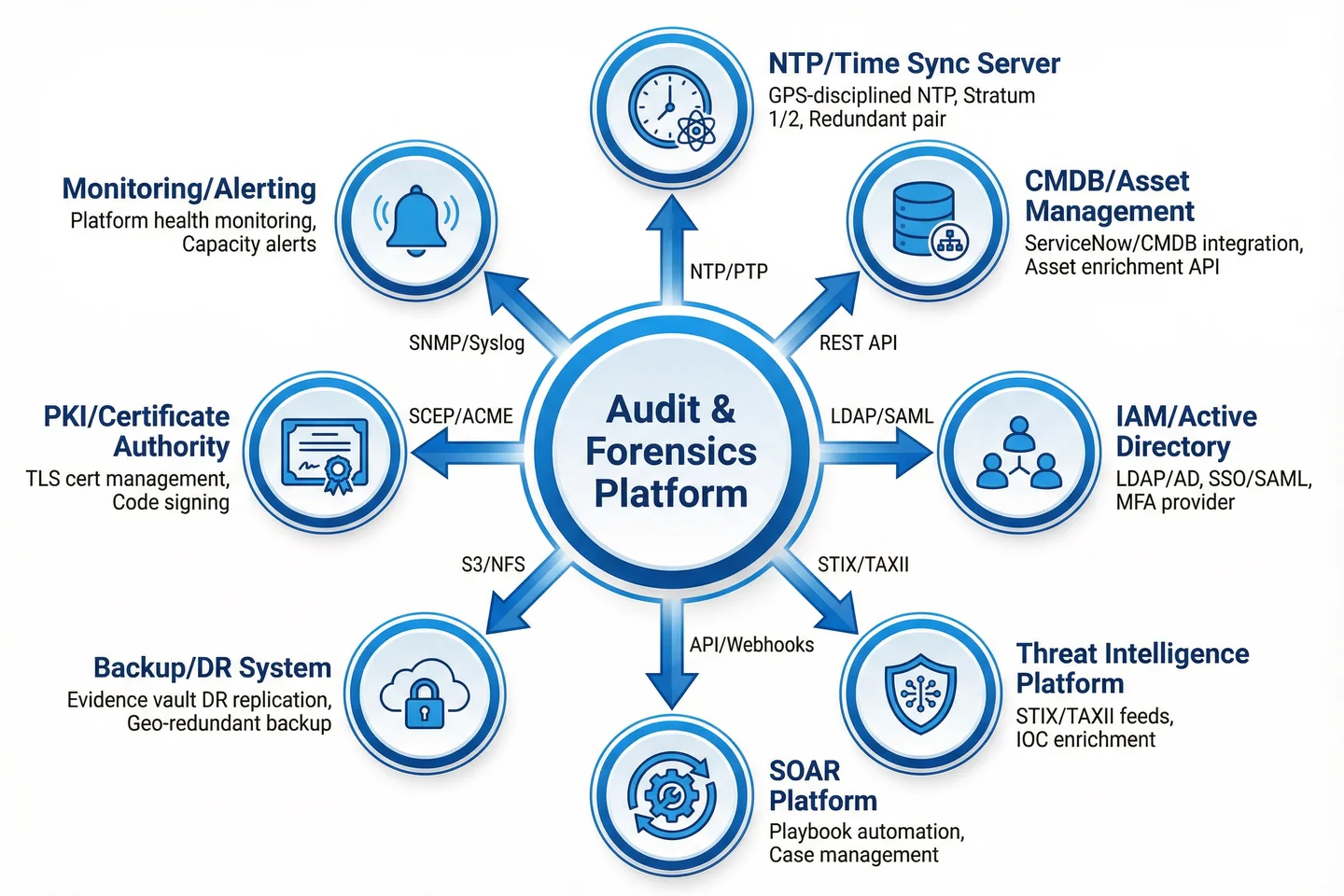
The audit and forensics platform does not operate in isolation. It depends on eight categories of supporting systems to deliver its full capabilities — from accurate time synchronization that underpins evidence timelines, to threat intelligence feeds that enrich detection, to backup systems that protect the evidence vault itself. The diagram below shows all supporting systems integrated around the central platform, with their integration protocols.
7.2 Supporting System Requirements
Each supporting system has specific integration requirements that must be met for the platform to function correctly. The table below defines the mandatory requirements, integration protocols, and failure mode handling for each supporting system. These requirements must be verified during acceptance testing and monitored continuously in production.
| Supporting System | Integration Protocol | Mandatory Requirements | Failure Mode Handling | SLA Dependency |
|---|---|---|---|---|
| NTP / Time Sync Server | NTP v4 with NTS authentication; PTP IEEE 1588 optional | Stratum 1 or 2; GPS-disciplined primary; redundant pair; NTS authentication mandatory; maximum skew ≤1s across all platform components | Automatic failover to secondary NTP server; alert on skew >100ms; log time source changes | Critical — evidence timeline integrity depends on NTP availability |
| CMDB / Asset Management | REST API (ServiceNow, Jira, or custom CMDB) | Asset enrichment API with hostname → IP → owner → criticality mapping; real-time or near-real-time sync (≤15 min lag); read-only integration from platform side | Cache last-known-good CMDB data; alert on sync failure; degrade gracefully with reduced enrichment | High — asset context enrichment for alert triage |
| IAM / Active Directory | LDAP/LDAPS; SAML 2.0 for SSO; RADIUS for MFA | LDAPS (TLS) mandatory; service account with read-only LDAP access; SSO for all platform admin interfaces; MFA enforcement at IdP level | Local emergency accounts for break-glass; alert on LDAP connectivity failure; session timeout on IdP failure | Critical — all platform authentication depends on IAM |
| Threat Intelligence Platform | STIX/TAXII 2.1; REST API for commercial feeds | Minimum 3 threat intel feeds (1 commercial, 1 ISAC, 1 open-source); IOC refresh ≤1 hour; STIX 2.1 format; integration with SIEM detection rules | Continue with cached IOCs on feed failure; alert on feed staleness >4 hours; manual IOC import fallback | Medium — enriches detection but not critical path |
| SOAR Platform | REST API / Webhooks; SIEM alert forwarding | Bidirectional API for case creation and status updates; playbook trigger on SIEM alert; evidence package export to SOAR case; response action feedback to SIEM | Queue alert forwarding on SOAR unavailability; alert on queue depth; manual triage fallback | High — automated response depends on SOAR |
| Backup / DR System | S3-compatible API for evidence vault replication; NFS for SIEM config backup | Evidence vault replication to geo-redundant site; RPO ≤1 hour; RTO ≤4 hours; SIEM configuration backup daily; quarterly DR test required | Alert on replication lag >1 hour; automatic retry with exponential backoff; DR failover procedure documented | Critical — evidence vault DR depends on backup system |
| PKI / Certificate Authority | SCEP for automated certificate enrollment; ACME for web certificates; PKCS#12 for manual | Internal CA for all platform mTLS certificates; 2-year certificate lifetime; automated renewal 30 days before expiry; CRL/OCSP for revocation | Alert on certificate expiry <30 days; emergency manual renewal procedure; CRL caching for OCSP failure | High — all mTLS depends on PKI |
| Monitoring / Alerting | SNMP v3; syslog/TLS; Prometheus metrics; REST API | Platform health metrics exported to monitoring system; capacity alerts at 80% thresholds; availability monitoring for all platform components; separate monitoring channel from SIEM | Platform self-monitoring as fallback; alert on monitoring connectivity failure; separate alerting path from primary SIEM | High — platform health visibility depends on monitoring |
7.3 Integration Testing Requirements
All supporting system integrations must be verified through structured integration testing before the platform is accepted into production. The following test cases cover the critical integration paths and failure modes. Each test must be documented with pass/fail criteria and evidence of successful execution.
| Test Case | Integration | Test Procedure | Pass Criteria |
|---|---|---|---|
| TC-INT-01 | NTP time sync | Verify NTP sync status on all platform components; introduce artificial skew; verify alert triggers | All components sync to NTP; skew <1s; alert fires at 100ms skew |
| TC-INT-02 | LDAP/SSO authentication | Login to all platform interfaces via SSO; verify MFA enforcement; test break-glass account | SSO login succeeds; MFA required; break-glass account accessible |
| TC-INT-03 | Threat intel IOC enrichment | Inject known-malicious IOC into log stream; verify SIEM alert with TI enrichment | Alert fires within 5 minutes; IOC context visible in alert |
| TC-INT-04 | SOAR alert forwarding | Trigger SIEM alert; verify SOAR case creation; verify playbook execution; verify feedback to SIEM | Case created within 2 minutes; playbook executes; SIEM case status updated |
| TC-INT-05 | Evidence vault DR replication | Write test object to evidence vault; verify replication to DR site within RPO; test DR failover | Object replicated within 1 hour; DR failover completes within 4 hours |
| TC-INT-06 | PKI certificate renewal | Verify certificate expiry monitoring; simulate expiry alert; test automated renewal via SCEP | Alert fires at 30 days; automated renewal succeeds; no service interruption |