Tools & Accessories
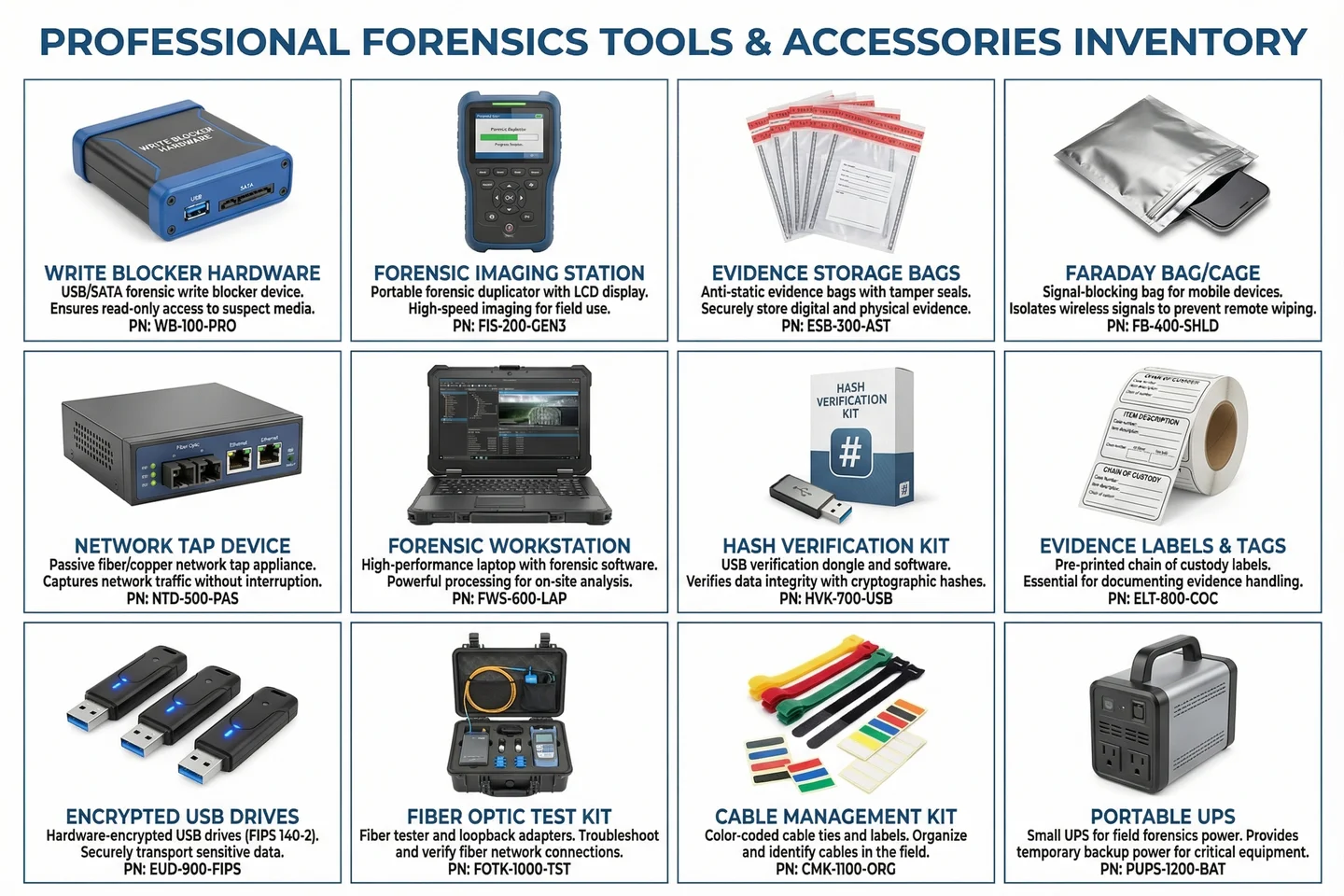
Complete accessories and tools inventory for network security audit and digital forensics deployments, including field forensics kits, evidence handling supplies, and network analysis tools.
8.1 Accessories & Tools Inventory
A complete audit and forensics deployment requires not only the core platform components described in Chapter 5, but also a set of specialized accessories and field tools that support evidence collection, integrity verification, and field investigations. The inventory below covers all categories of accessories required for a production-ready deployment, from hardware write blockers for safe media acquisition to Faraday bags for mobile device isolation.
8.2 Accessories Bill of Materials
The following bill of materials provides the complete accessories list for a standard enterprise deployment. Quantities are specified for the medium deployment scale (2,000–8,000 endpoints); adjust proportionally for small or large deployments. All items should be procured before the installation phase begins to avoid delays.
| Item | Part Number | Category | Qty (Medium) | Purpose | Mandatory |
|---|---|---|---|---|---|
| Write Blocker Hardware (USB/SATA) | WB-100-PRO | Evidence Collection | 4 | Safe media acquisition without write contamination | Yes |
| Forensic Imaging Station | FIS-200-GEN3 | Evidence Collection | 2 | High-speed forensic duplication in field | Yes |
| Evidence Storage Bags (pack/100) | ESB-300-AST | Evidence Handling | 10 packs | Anti-static tamper-evident evidence storage | Yes |
| Faraday Bag / Cage (mobile) | FB-400-SHLD | Evidence Handling | 6 | Signal isolation for mobile devices during seizure | Yes |
| Network TAP Device (1G copper) | NTD-500-PAS | Network Analysis | 4 | Passive in-line network capture without disruption | Yes |
| Network TAP Device (10G fiber) | NTD-510-FIB | Network Analysis | 4 | Passive fiber TAP for high-speed segments | Yes |
| Forensic Workstation (laptop) | FWS-600-LAP | Analysis Tools | 4 | Field forensic analysis and evidence processing | Yes |
| Hash Verification Kit | HVK-700-USB | Integrity Verification | 4 | Cryptographic hash verification of evidence files | Yes |
| Evidence Labels & Tags (roll/500) | ELT-800-COC | Chain of Custody | 4 rolls | Pre-printed chain-of-custody labels with barcode | Yes |
| Encrypted USB Drive (64GB, FIPS 140-2) | EUD-900-FIPS | Secure Transport | 10 | Secure evidence transport between sites | Yes |
| Fiber Optic Test Kit | FOTK-1000-TST | Network Tools | 2 | Fiber continuity and loss testing for TAP installation | Recommended |
| Cable Management Kit | CMK-1100-ORG | Installation | 4 | Color-coded cable organization for rack installation | Recommended |
| Portable UPS (1500VA) | PUPS-1200-BAT | Power | 2 | Field power backup for forensic equipment | Recommended |
| Anti-Static Mat & Wrist Strap Kit | ESD-1300-KIT | Safety | 4 | ESD protection during hardware evidence handling | Recommended |
| Evidence Seal Tape (roll/50m) | EST-1400-TAM | Evidence Handling | 10 rolls | Tamper-evident sealing for evidence containers | Yes |
8.3 Software Tools Inventory
In addition to hardware accessories, a set of software forensic tools must be licensed and deployed on forensic workstations. The following table lists the recommended software tools for each forensic function, with licensing model and deployment notes. All software tools must be version-controlled and their hashes documented in the case record for each investigation.
| Tool Category | Recommended Tools | License Model | Primary Use Case |
|---|---|---|---|
| Disk Imaging | FTK Imager, dd/dcfldd, Guymager | Commercial / Open-source | Forensic disk image acquisition with hash verification |
| Memory Forensics | Volatility 3, Rekall | Open-source | RAM dump analysis, process/network artifact extraction |
| Network Forensics | Wireshark, NetworkMiner, Zeek | Open-source | PCAP analysis, protocol decoding, connection reconstruction |
| Log Analysis | Splunk, Elastic/Kibana, Chainsaw | Commercial / Open-source | Windows Event Log analysis, timeline reconstruction |
| Timeline Analysis | Plaso/log2timeline, Autopsy | Open-source | Multi-source timeline creation and analysis |
| Hash Verification | HashMyFiles, md5deep, sha256sum | Open-source | Evidence integrity verification and hash catalog management |
| Evidence Management | Autopsy, Sleuth Kit, CAINE | Open-source | Case management, evidence organization, report generation |
| Malware Analysis | FLARE VM, Cuckoo Sandbox, YARA | Open-source | Static and dynamic malware analysis in isolated environment |